Spring Sale Limited Time 75% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = simple75
Pass the Cisco CyberOps Professional 300-215 Questions and answers with Dumpstech
What are two features of Cisco Secure Endpoint? (Choose two.)
A cybersecurity analyst is analyzing a complex set of threat intelligence data from internal and external sources. Among the data, they discover a series of indicators, including patterns of unusual network traffic, a sudden increase in failed login attempts, and multiple instances of suspicious file access on the company's internal servers. Additionally, an external threat feed highlights that threat actors are actively targeting organizations in the same industry using ransomware. Which action should the analyst recommend?
A cybersecurity analyst must evaluate files from an endpoint in an enterprise network. The antivirus software on the endpoint flagged a suspicious file during a routine scan On initial evaluation the file did not match any known signatures in the antivirus database, but exhibited unusual network behavior during dynamic analysis Which step should the analyst take next?
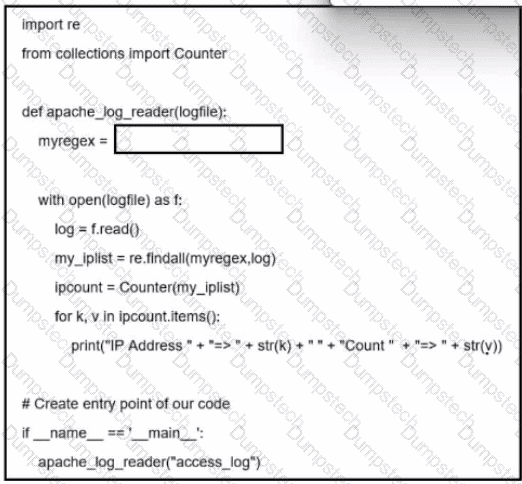
Refer to the exhibit. A network administrator creates an Apache log parser by using Python. What needs to be added in the box where the code is missing to accomplish the requirement?
A network host is infected with malware by an attacker who uses the host to make calls for files and shuttle traffic to bots. This attack went undetected and resulted in a significant loss. The organization wants to ensure this does not happen in the future and needs a security solution that will generate alerts when command and control communication from an infected device is detected. Which network security solution should be recommended?
An incident response analyst is preparing to scan memory using a YARA rule. How is this task completed?
An attacker modifies a malicious file named TOPSECRET0523619132 by changing its file extension from a .png to a doc in an attempt to evade detection. Which technique is being used to disguise the file?
What is a concern for gathering forensics evidence in public cloud environments?
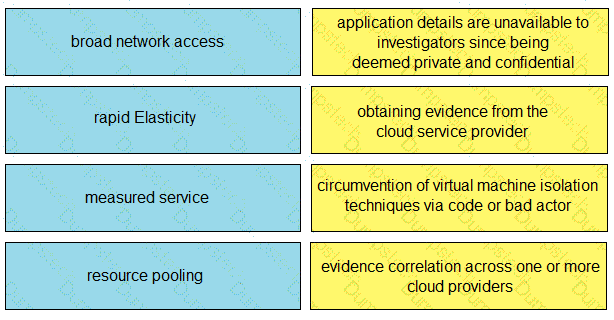
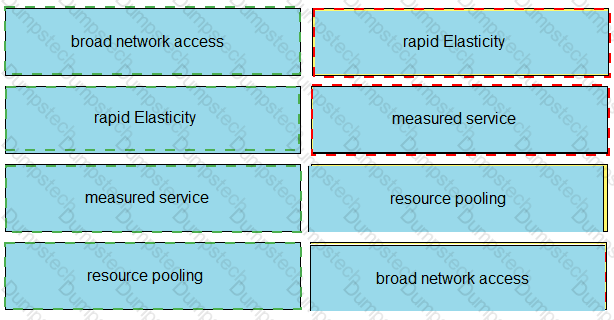
Drag and drop the cloud characteristic from the left onto the challenges presented for gathering evidence on the right.