CrowdStrike Certification Exams Pack
Everything from Basic, plus:
- Exam Name: CrowdStrike Certified Falcon Hunter
- 60 Questions Answers with Explanation Detail
- Total Questions: 60 Q&A's
- Single Choice Questions: 60 Q&A's
Students Passed
Average Score
Questions came word for word
Years Teaching
Explore other related CrowdStrike exams to broaden your certification path. These certifications complement your skills and open new opportunities for career growth.
If you're looking to secure CCFH (CCFH-202b) certification, remember there's no royal path to it. It's your prep for this exam that can make the difference. Stay away from those low-quality exam PDFs and unreliable dumps that have no credibility.
To save you from frustration, Dumpstech comes with a comprehensive prep system that is clear, effective, and built to help you succeed without the least chance of failure.
It's overwhelmingly recommended by thousands of Dumpstech's loyal customers as practical, relevant and intuitively crafted to match the candidates' actual exam needs.
Dumpstech's CrowdStrike exam CCFH-202b questions are designed to deliver you the essence of the entire syllabus. Each question mirrors the real exam format and comes with an accurate and verified answer. Dumpstech's prep system is not mere cramming; it is crafted to add real information and impart deep conceptual understanding to the exam candidates.
Dumpstech's smart testing engine generates multiple mock tests to develop familiarity with the real exam format and learn thoroughly the most significant from the perspective of CrowdStrike CCFH-202b real exam. They also support you to revise the syllabus and enhance your efficiency to answer all exam questions within the time limit.
Dumpstech offers you the most authentic, accurate, and current information that liberates you from the hassle of searching for any other study resource. This comprehensive resource equips you perfectly to develop confidence and clarity to answer exam queries.
Dumpstech's authentic and up-to-date content guarantees you success in the CrowdStrike Certified Falcon Hunter certification exam. If you perchance you lose your exam despite your reliance on Dumpstech's exam questions PDF, Dumpstech doesn't leave you alone. You have the option of taking back refund of your money or try a different exam paying no additional amount.
If you want to crack the CrowdStrike Certified Falcon Hunter (CCFH-202b) exam in one go, your journey starts here. Dumpstech is your real ally that gets you certified fast with the least possibility of losing your chance.
You see a large number of command-line processes calling back to an unusual domain that you are reviewing with the Bulk Domain Investigate dashboard. What should your next steps be?
|
B
|
|---|
|
Explanation
Comprehensive and Detailed 150 to 250 words of Explanation From Falcon Hunter Topics documents: The best answer is B because it reflects the normal Falcon Investigate workflow: first review the domain’s reputation and associated network connection history to determine whether the observed activity is suspicious or malicious before taking containment actions. CrowdStrike’s official Falcon Hunter training material states that analysts should know how to perform a Bulk Domain search and understand the information it provides as part of proactive investigations , which supports using the dashboard to validate and analyze the domain activity before escalating to blocking or broader scoping actions. Option A is not the strongest immediate next step because placing a firewall block before validating the domain’s reputation and reviewing the observed history can interrupt legitimate activity and move too quickly into response before investigation is complete. Option C can be a useful follow-up step after initial triage, especially if the domain appears suspicious and you want to understand broader host exposure, but it is secondary to first examining the reputation and connection history already surfaced through the Bulk Domain Investigate workflow. Based on CrowdStrike’s investigative approach, B is the most defensible and methodical answer because it uses the available domain-focused telemetry first and supports evidence-based decision-making. |
You receive an alert for the following process tree:
w3wp.exe > powershell.exe > cmd.exe > whoami.exe > net1.exe Which of the following describes what has occurred?
|
A
|
|---|
|
Explanation
In Detection Analysis , the process w3wp.exe is a critical focal point as it is the IIS (Internet Information Services) Worker Process. Under normal operating conditions, w3wp.exe should be handling web requests and should almost never spawn interactive shells like powershell.exe or cmd.exe. When a process tree shows a web worker process spawning a shell, it is a high-confidence Indicator of Attack (IOA) typically associated with a Web Shell or a successful exploitation of a web application vulnerability. The subsequent commands—whoami.exe and net1.exe—are classic post-exploitation Reconnaissance tools. whoami is used by an attacker to determine the privileges of the service account they have compromised, while net1 is used to enumerate local or domain users and groups to identify potential targets for lateral movement. The progression from a web process to a shell and then to identity/network discovery is a definitive behavioral pattern of a remote attacker establishing a foothold and performing initial situational awareness. While an administrator might use these tools for troubleshooting (Option B), they would typically do so via a direct login or a remote management session, not through the w3wp.exe parent tree. Recognizing this specific lineage is essential for hunters to differentiate between legitimate administrative maintenance and an active, live-site compromise requiring immediate intervention and containment. |
Refer to the image.
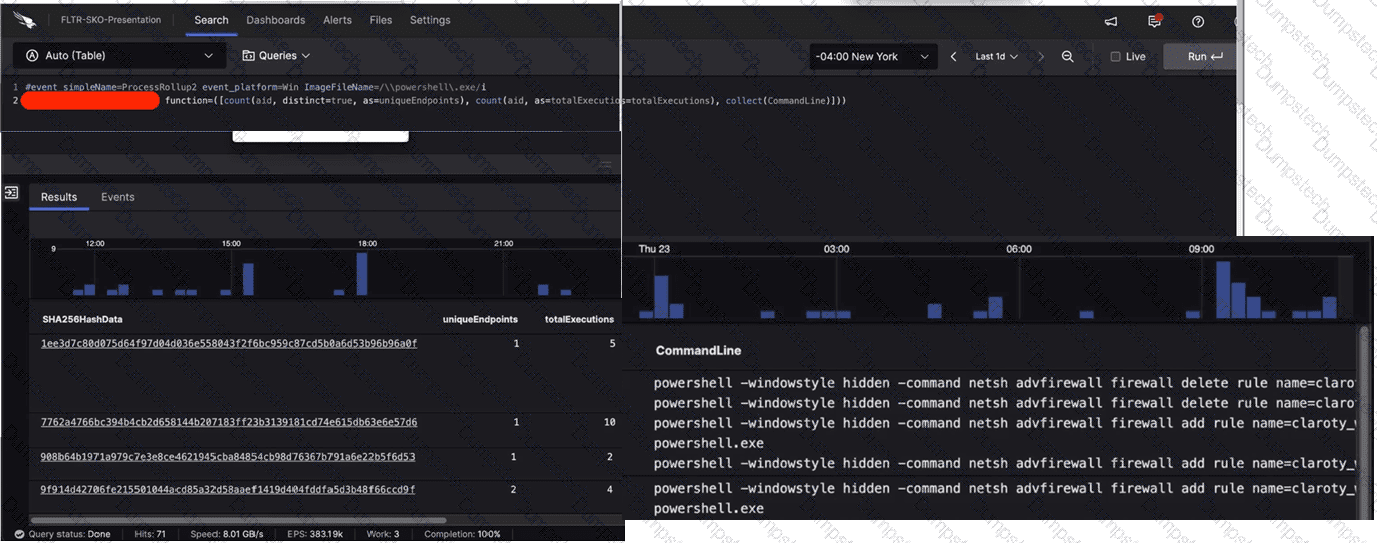
What aggregate function in the CrowdStrike Query Language (CQL) was used to provide the filtered results?
|
B
|
|---|
|
Explanation
In the CrowdStrike Query Language (CQL) used within the LogScale-powered Advanced Event Search, the groupBy() function is the essential tool for data aggregation and summarization. As observed in the first image, Line 2 of the query (partially obscured) utilizes the function= parameter to define multiple aggregate calculations, such as count(aid, distinct=true) and count(aid). This syntax is the hallmark of a groupBy statement. The results shown in the subsequent images display a table where each row is unique to a specific SHA256HashData . This indicates that the data has been grouped by that specific field to provide a summary of its activity across the environment. The groupBy function allows a hunter to take millions of individual process events and collapse them into a readable format that highlights uniqueEndpoints and totalExecutions per file hash. This methodology is fundamental to Hunting Analytics , specifically for performing Least Frequency Analysis . By grouping by the hash and counting the unique endpoints, an analyst can quickly identify binaries that are running on only one or two systems—a common characteristic of targeted malware or custom hacking tools. While functions like table (Option C) are used to format the final display and eval (Option A) is used for field transformations, only groupBy provides the structural aggregation required to generate the multi-column statistical overview seen in the results. |
See how DumpsTech helps candidates pass with confidence.
Stay ahead in your career with the latest certification exams from leading vendors. DumpsTech brings you newly released exams with reliable study resources to help you prepare confidently.
Find answers to the most common questions about the CrowdStrike CCFH-202b exam, including what it is, how to prepare, and how it can boost your career.
The CrowdStrike CCFH-202b certification is a globally-acknowledged credential that is awarded to candidates who pass this certification exam by obtaining the required passing score. This credential attests and validates the candidates' knowledge and hands-on skills in domains covered in the CrowdStrike CCFH-202b certification syllabus. The CrowdStrike CCFH-202b certified professionals with their verified proficiency and expertise are trusted and welcomed by hiring managers all over the world to perform leading roles in organizations. The success in CrowdStrike CCFH-202b certification exam can be ensured only with a combination of clear knowledge on all exam domains and securing the required practical training. Like any other credential, CrowdStrike CCFH-202b certification may require periodic renewal to stay current with new innovations in the concerned domains.