Spring Sale Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = simple70
Pass the Huawei HCIA-Security H12-711_V4.0 Questions and answers with Dumpstech
Under normal circumstances, the Emai1 protocols we often talk about include ____, POP3, and SMTP.[fill in the blank]*
Which of the following descriptions about the heartbeat interface is wrong ( )?
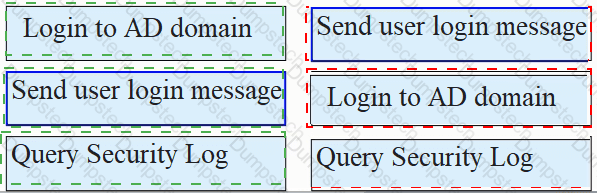
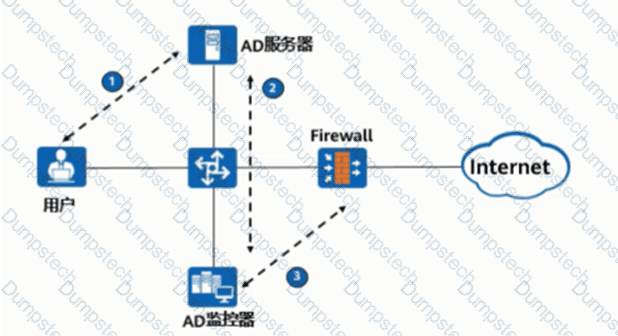
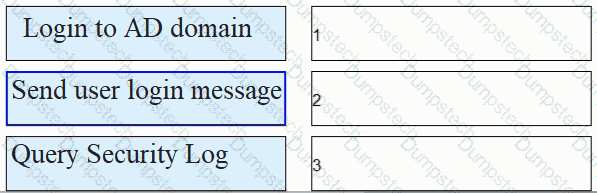
As shown in the figure, the process of AD single sign-on (querying the security log mode of AD server), please match the corresponding operation process.
3-tuple NAT allows external devices to proactively access internal PCs through translated addresses and ports. Even if no security policy is configured on the firewall, the firewall allows such access packets to pass through.
Which of the following is the numbering range of Layer 2 ACLs?
The following description of the construction of a digital certificate, which item is wrong
Which of the following is the correct sequence for incident response management
1. Detection 2 Report 3 Mitigation 4 Lessons learned 5 Fix 6 Recovery 7 Response
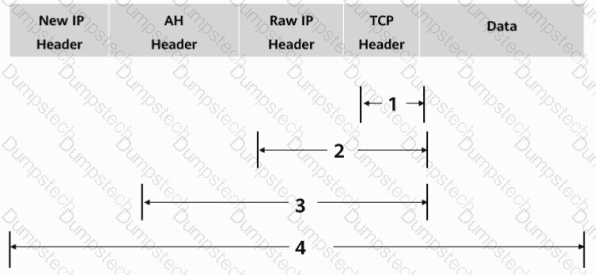
As shown in the figure, what is the authentication range of the AH protocol in tunnel mode?
IPS signatures describe the characteristics of attack behaviors on the network. The firewall detects and defends against attacks by comparing data flows with IPS signatures.
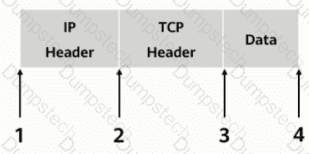
As shown, in transmission mode, which of the following locations should the AH header be inserted in?